The modern world of cybersecurity is at a turning point. Vectra AI, a recognized leader in detecting and responding to hybrid and multi-cloud threats, has released its “2023 State of Threat Detection Report.” This document sheds light on a phenomenon Vectra AI terms the “spiral of more” – a challenge systematically hindering Security Operations Center (SOC) teams from effectively protecting their organizations against increasingly pervasive cyberattacks.
Modern Security Operations (SecOps) teams face the incredibly complex task of defending against cyberattacks that are not only becoming more sophisticated but also strikingly swift. However, as the report reveals, the intricate interplay between people, processes, and technologies at their disposal makes cyber defense increasingly vulnerable to new challenges. The continuously expanding attack surface, coupled with rapidly evolving attacker methods and an increasing workload for SOC analysts, creates a true “vicious spiral.” This prevents security teams from effectively defending their organizations, threatening their cyber resilience. The report is based on a detailed survey of 2,000 SecOps analysts, explaining why the current approach to security operations is unsustainable in the long run.
The “Spiral of More”: Core Challenges for Security Teams
The “spiral of more” concept from Vectra AI captures the growing difficulties faced by security teams. It is characterized by several critical aspects:
Economic Losses from Manual Alert Triage
Manual alert triage costs organizations enormous sums. According to the report, in the U.S. alone, this figure amounts to a staggering $3.3 billion annually. Security analysts are tasked with detecting, investigating, and responding to threats as quickly and effectively as possible, all while contending with an expanding attack surface and thousands of daily security alerts. This creates constant pressure and makes SOC work extremely stressful.
Growing Attack Surface and Alert Volume
- 63% of respondents report that their attack surface has increased in the last three years. This includes the shift to hybrid and multi-cloud environments, the proliferation of IoT devices, and remote work.
- On average, SOC teams receive 4,484 alerts daily, which equates to approximately 3 alerts per minute during a workday.
- Analysts spend nearly three hours per day manually triaging alerts. This is a tremendous amount of time that could otherwise be spent on more strategic tasks, such as proactive threat hunting or improving defensive mechanisms.
Overload and False Positives: Analyst Frustration
- 67% of daily alerts go unaddressed because security analysts are simply unable to cope with such an overwhelming volume.
- Furthermore, 83% report that these unaddressed alerts are false positives and not worth the time spent. This not only leads to decreased productivity but also erodes trust in security systems.
Analyst Burnout: A Hidden Risk to the Security Industry
Despite the increasingly widespread adoption of artificial intelligence and automation tools, the security industry still requires a significant number of human personnel to interpret data, launch investigations, and take corrective actions based on the information they convey. This human factor, combined with the challenges described above, leads to a significant risk of analyst burnout, which can have devastating long-term consequences for the industry.
Shocking Burnout Statistics:
- Two-thirds of security analysts report that, when faced with alert overload and repetitive routine tasks, they are considering leaving or actively leaving their jobs. This figure is alarming, considering the global shortage of qualified cybersecurity professionals.
- Despite 74% of respondents stating that their job meets their expectations, 67% are still considering leaving or actively leaving their job. This indicates deep systemic problems that go beyond simple job satisfaction.
- Of the analysts considering leaving or actively leaving their position, 34% state that they lack the necessary tools to effectively protect their organization. This is a direct call to solution providers to improve their products.
- 55% of analysts state that they are so busy they feel like they are doing the work of multiple people.
- 52% believe that working in the security sector is not a long-term viable career option. This is a very disturbing trend that threatens the future of the industry.
Kevin Kennedy, Senior Vice President of Product at Vectra AI, emphasized: “As enterprises shift to hybrid and multi-cloud environments, security teams are constantly facing a greater attack surface, more attacker evasion techniques, more noise, more complexity, and more hybrid attacks. The current approach to threat detection is not working, and the results of this report prove that a surplus of disparate, siloed tools creates too much detection noise that SOC analysts cannot successfully manage, and instead creates a noisy environment perfect for attacker intrusion. As an industry, we cannot continue to feed this ‘spiral of more,’ and it’s time to hold security vendors accountable for the efficacy of their signal. The more effective the threat signal, the more cyber-resilient and effective the SOC becomes.”
Vectra AI: An Effective Solution for Ukrainian Cybersecurity with NWU
Thanks to NWU, the official distributor of Vectra AI in Ukraine, domestic organizations now have access to the advanced NDR (Network Detection and Response) solution from a global leader. This solution is an integral part of the SOC triad – a fundamental concept of modern cybersecurity.
Vectra AI: A Key Component of the SOC Triad
The SOC triad represents a comprehensive approach to cybersecurity, combining three core elements to ensure maximum protection:
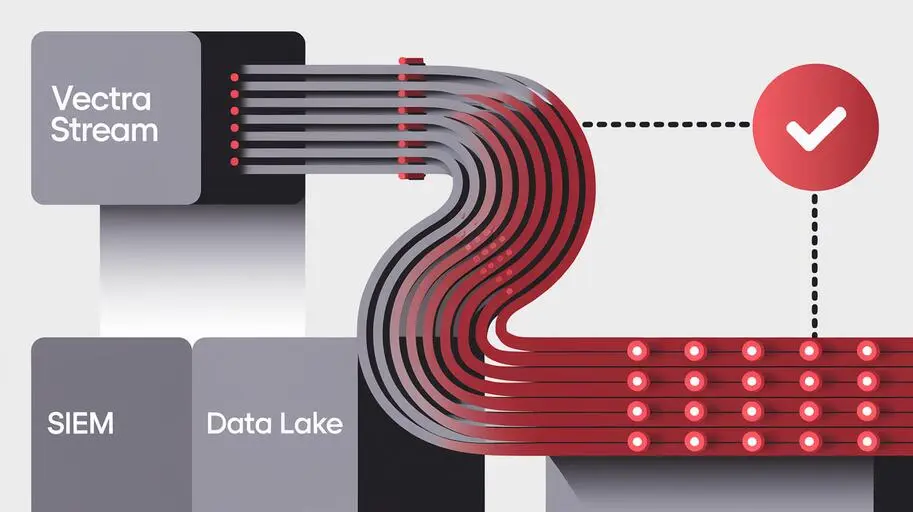
- SIEM (Security Information and Event Management): A system for collecting, aggregating, and analyzing security logs and events from all systems and devices within the infrastructure. SIEM provides a centralized data repository for analysis, helping SOC teams detect anomalies and correlate events to identify complex attacks. Examples include IBM Security QRadar and Splunk Enterprise Security.
- EDR (Endpoint Detection and Response): A solution that provides continuous monitoring and recording of activity on endpoints (workstations, servers, mobile devices). EDR enables detection of suspicious behavior, real-time threat response (e.g., isolating a compromised host), and detailed investigations. Examples include CrowdStrike Falcon and SentinelOne.
- NDR (Network Detection and Response) from Vectra AI: This component specializes in real-time network traffic analysis, allowing for the detection of threats that might have bypassed traditional security tools (e.g., firewalls or antiviruses). NDR from Vectra AI plays a critical role in detecting lateral movement of attackers within the network, anomalies in network device and protocol behavior, as well as hidden communication channels and data exfiltration. This is particularly important for hybrid and multi-cloud environments where traditional security measures may be ineffective. According to a Cisco study, 53% of companies consider NDR critically important for threat detection.
The synergy of these three components creates a comprehensive cyber defense system that provides full visibility, deep analysis, and rapid response to threats at all levels of the infrastructure.
Vectra AI’s Unique Approach to Threat Detection
Vectra AI is a leader in detecting and responding to hybrid cloud threats thanks to its unique approach, based on security artificial intelligence. Unlike most solutions that generate an excessive number of alerts about “anomalies” or “other” events, only Vectra optimizes AI to detect specific attacker methods – TTP (Tactics, Techniques, and Procedures), which are at the core of all real attacks.
The Vectra AI platform covers:
- Public Cloud: Monitoring and protecting your assets in AWS, Azure, Google Cloud.
- SaaS Applications: Detecting threats in Microsoft 365, Salesforce, and other critically important business applications.
- Identity Systems: Protecting Active Directory, Azure AD, and other identity services from compromise.
- Network Infrastructure: Comprehensive monitoring of both on-premises and cloud networks to detect suspicious activity.
The resulting highly accurate threat signal and clear context enable cybersecurity teams to react to threats faster and prevent potential attacks from becoming actual breaches. This reduces the risks associated with data breaches, financial losses, and reputational damage.
Protecting Against Key Cyber Threats with Vectra AI
Organizations worldwide rely on the Vectra AI platform and services to achieve resilience against the most dangerous cyber threats and neutralize them, such as:
- Ransomware: Rapid detection and blocking of ransomware activity in the early stages of an attack, which can prevent data encryption and ransom demands. According to Cybersecurity Ventures, global ransomware damages are expected to reach $30 billion by 2025.
- Supply Chain Attacks: Detecting anomalies that may indicate a compromise of suppliers or integrated components, through which attackers can penetrate your network.
- Credential Theft: Proactive detection of attempts to steal or use compromised credentials, which is one of the most common attack vectors for gaining access to sensitive systems. According to the Verizon DBIR 2024, credential compromise accounts for 45% of data breaches.
- Other Cyberattacks: Providing comprehensive protection against a wide range of modern and future threats, including fileless attacks, zero-day attacks, and targeted APT group attacks, which are constantly evolving and adapting.
Contact NWU: Strengthening Your Cybersecurity
If your organization aims to strengthen its cybersecurity and effectively counter growing cyber threats, then the Vectra AI solution is an ideal choice. To buy NDR for SOC or to request a test of the Vectra AI solution in Ukraine, please contact NWU. As an official distributor, we offer not only advanced technologies but also a full range of expert support that will help you implement and utilize this powerful solution as effectively as possible.
This is your chance to significantly enhance the efficiency of your security team, reduce the risk of analyst burnout, and reliably protect your digital assets, ensuring resilience against the most complex cyber threats.
Learn more about Vectra AI on the vendor’s website: https://www.vectra.ai/